Suppose we have a wheel cipher device that has 4 wheels. Compare the theoretical and practical...
Suppose we have a wheel cipher device that has 4 wheels. Compare the theoretical and practical security of this wheel cipher device with Vigenère cipher with block length equals to 4.
Homework Answers
The Vigenère Cipher
The Vigenère cipher, was invented by a Frenchman, Blaise de Vigenère in the 16th century. It is a polyalphabetic cipher because it uses two or more cipher alphabets to encrypt the data. In other words, the letters in the Vigenère cipher are shifted by different amounts, normally done using a word or phrase as the encryption key .
Unlike the monoalphabetic ciphers, polyalphabetic ciphers are not susceptible to frequency analysis, as more than one letter in the plaintext can be represented by a single letter in the encryption.
At the time, and for many centuries since its invention, the Vigenère Cipher was renowned for being a very secure cipher, and for a very long time it was believed to be unbreakable. It was this thought that earned it the nickname "le chiffre indéchiffrable" (French for "the unbreakable cipher"). Although this is not true (it was fully broken by Friedrich Kasiski in 1863), it is still a very secure cipher in terms of paper and pen methods, and is usable as a field cipher.
The Vigenère Square:-
Blaise de Vigenère developed a square to help encode messages. Reading along each row, you can see that it is a really a series of Caesar ciphers the first has a shift of 1, the second a shift of 2 and so.
| A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | |
| A | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z |
| B | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A |
| C | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B |
| D | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C |
| E | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D |
| F | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E |
| G | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F |
| H | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G |
| I | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H |
| J | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I |
| K | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J |
| L | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K |
| M | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L |
| N | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M |
| O | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N |
| P | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O |
| Q | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P |
| R | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q |
| S | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R |
| T | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S |
| U | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T |
| V | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U |
| W | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V |
| X | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W |
| Y | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X |
| Z | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y |
The Vigenère cipher uses this table in conjunction with a key to encipher a message.
So, if we were to encode a message using the key COUNTON, we write it as many times as necessary above our message. To find the encryption, we take the letter from the intersection of the Key letter row, and the Plaintext letter column.
| Key | C | O | U | N | T | O | N | C | O | U | N | T | O | N |
| Plaintext | V | I | G | E | N | E | R | E | C | I | P | H | E | R |
| Encryption | X | W | A | R | G | S | E | G | Q | C | C | A | S | E |
To decipher the message, the recipient needs to write out the key above the ciphertext and reverse the process.
The maths behind the Vigenère cipher can be written as
follows:
To encrypt a message: Ca = Ma + Kb (mod 26)
To decrypt a message: Ma = Ca – Kb (mod 26)
(Where C = Code, M = Message, K = Key, and where a = the ath
character of the message bounded by the message, and b is the bth
character of the Key bounded by the length of the key.)
In a Caesar cipher, each letter of the alphabet is shifted along some number of places. For example, in a Caesar cipher of shift 3, A would become D, B would become E, Y would become B and so on. The Vigenère cipher has several Caesar ciphers in sequence with different shift values.
To encrypt, a table of alphabets can be used, termed a tabula recta, Vigenère square or Vigenère table. It has the alphabet written out 26 times in different rows, each alphabet shifted cyclically to the left compared to the previous alphabet, corresponding to the 26 possible Caesar ciphers. At different points in the encryption process, the cipher uses a different alphabet from one of the rows. The alphabet used at each point depends on a repeating keyword.
Security :-
My question is regarding the Vigenère cipher: It is my understanding that the security of this cipher is directly related to the length and security of the keys. Long and tightly secured keys bring this cipher on par with many more complex techniques.
Besides others (e.g. random key, key used only once) it depends on the proportion of cipher text length and key length how difficult it is to break the cipher. There are tools around that can break the cipher if cipher_text_length/key_length is 4 or greater.In some exceptional cases the proportion may be even 3. Thus the Vigenere cipher is rather insecure. But as already said by others: If the key length is equal to the cipher text length then the cipher is absolutely secure if the key is chosen completely randomly and is only used once. This will turn the cipher into a one time pad. Drawback: one time pads are difficult and ineffective to manage.
Discussion
The Vigenère Cipher was the biggest step in cryptography for over
1000 years. The idea of switching between ciphertext alphabets as
you encrypt was revolutionary, and an idea that is still used to
make ciphers more secure. One of the most famous examples of codes
and ciphers in history, the ENIGMA machine, is just a modified
polyalphabetic substitution cipher!
But why is the Vigenère Cipher so secure? What is it that makes this cipher better than the Mixed Alphabet Cipher? Let's take a look at an example. We shall encrypt the following text using the Mixed Alphabet Cipher and the Vigenère Cipher, both with the keyword encrypt.
Plain Text:-
Aged twenty six, Vigènere was sent to Rome on a diplomatic mission. It was here that he became acquainted with the writings of Alberti, Trithemius and Porta, and his interest in cryptography was ignited. For many years, cryptography was nothing more than a tool that helped him his diplomatic work, but at the age of thirty nine, Vigènere decided that he had amassed enough money to be able to abandon his career and concentrate on a life of study. It was only then that he began research into a new cipher.
Using the Mixed Alphabet we get:
ETYR QVYIQX OBW, UBTYIYMY VEO OYIQ QJ MJHY JI E RBKGJHEQBC HBOOBJI. BQ VEO AYMY QAEQ AY NYCEHY ECLSEBIQYR VBQA QAY VMBQBITO JP EGNYMQB, QMBQAYHBSO EIR KJMQE, EIR ABO BIQYMYOQ BI CMXKQJTMEKAX VEO BTIBQYR. PJM HEIX XYEMO, CMXKQJTMEKAX VEO IJQABIT HJMY QAEI E QJJG QAEQ AYGKYR ABH ABO RBKGJHEQBC VJMF, NSQ EQ QAY ETY JP QABMQX IBIY, UBTYIYMY RYCBRYR QAEQ AY AER EHEOOYR YIJSTA HJIYX QJ NY ENGY QJ ENEIRJI ABO CEMYYM EIR CJICYIQMEQY JI E GBPY JP OQSRX. BQ VEO JIGX QAYI QAEQ AY NYTEI MYOYEMCA BIQJ E IYV CBKAYM.
And using the Vigenère we get:
ETGU RLXRGA JGM, OMTGECGX ANU JCCM XB TFKT HR N FZNAHQNVZA BBWFKFL. XM ANU YCGX XUCK FT UIPCDC PVUHCZLIXH JKKF IAI JTZRXGKF QW YAUIEVZ, RGBXUGDGJL EAF GMGME, NPU FXL MAVVPTLX VP TPNIXBIIYEAC JCJ GVGMGGU. DDK QNPP WTTVF, EIWEMSTTRNWR ANU EMIAMAI DMGX XUCE Y IHSY VYYI AIYRVB WBQ UKJ BXIPBORRXV ABTB, ZJM EG VYC PZI BH KFXKXL PZLT, OMTGECGX HREZBTW XUCK FT AEQ CDYHLIQ GEMJZL ZQECN MS OG RZAX XB CSYCWSA JZQ RTVRGI YCW GBPTCCMVNVV MC T PVHV MU LXHFP. GI PEF QEJN MLRP KFPM LR DVEPG VRUVYGVL VPKM P GIJ EZNWXV.
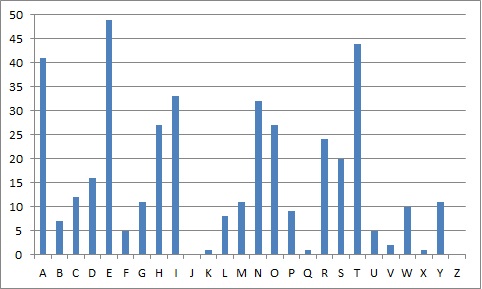
The Frequency distribution of the plaintext. 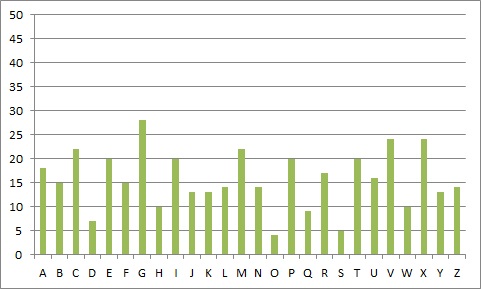
The Frequency distribution of the ciphertext using the Vigenère Cipher. |
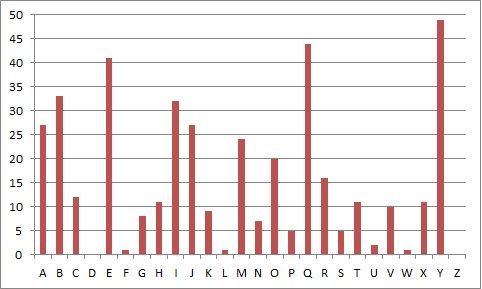
The Frequency distribution of the ciphertext using the Mixed Alphabet Cipher. These frequency distributions show how many times each letter appears in the relevent text. We can see a clear relationship between the top two, with the same peaks just in different places. |
The final distribution, for the Vigenère Cipher, is different to the others, and the distribution of letters is much more smoothed out. And even though there is a little bit of a peak at "G" (which we might think to be "e"), in the penultimate word "new" is "GIJ", so "G" is "n", but in the first word "aged" is "ETGU" so "G" is "e". This shows that the same letter can be achieved by different plaintext letters.
The Vigenère Cipher
The Vigenère cipher, was invented by a Frenchman, Blaise de Vigenère in the 16th century. It is a polyalphabetic cipher because it uses two or more cipher alphabets to encrypt the data. In other words, the letters in the Vigenère cipher are shifted by different amounts, normally done using a word or phrase as the encryption key .
Unlike the monoalphabetic ciphers, polyalphabetic ciphers are not susceptible to frequency analysis, as more than one letter in the plaintext can be represented by a single letter in the encryption.
At the time, and for many centuries since its invention, the Vigenère Cipher was renowned for being a very secure cipher, and for a very long time it was believed to be unbreakable. It was this thought that earned it the nickname "le chiffre indéchiffrable" (French for "the unbreakable cipher"). Although this is not true (it was fully broken by Friedrich Kasiski in 1863), it is still a very secure cipher in terms of paper and pen methods, and is usable as a field cipher.
The Vigenère Square:-
Blaise de Vigenère developed a square to help encode messages. Reading along each row, you can see that it is a really a series of Caesar ciphers the first has a shift of 1, the second a shift of 2 and so.
| A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | |
| A | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z |
| B | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A |
| C | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B |
| D | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C |
| E | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D |
| F | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E |
| G | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F |
| H | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G |
| I | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H |
| J | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I |
| K | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J |
| L | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K |
| M | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L |
| N | N | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M |
| O | O | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N |
| P | P | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O |
| Q | Q | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P |
| R | R | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q |
| S | S | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R |
| T | T | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S |
| U | U | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T |
| V | V | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U |
| W | W | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V |
| X | X | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W |
| Y | Y | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X |
| Z | Z | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y |
The Vigenère cipher uses this table in conjunction with a key to encipher a message.
So, if we were to encode a message using the key COUNTON, we write it as many times as necessary above our message. To find the encryption, we take the letter from the intersection of the Key letter row, and the Plaintext letter column.
| Key | C | O | U | N | T | O | N | C | O | U | N | T | O | N |
| Plaintext | V | I | G | E | N | E | R | E | C | I | P | H | E | R |
| Encryption | X | W | A | R | G | S | E | G | Q | C | C | A | S | E |
To decipher the message, the recipient needs to write out the key above the ciphertext and reverse the process.
The maths behind the Vigenère cipher can be written as
follows:
To encrypt a message: Ca = Ma + Kb (mod 26)
To decrypt a message: Ma = Ca – Kb (mod 26)
(Where C = Code, M = Message, K = Key, and where a = the ath
character of the message bounded by the message, and b is the bth
character of the Key bounded by the length of the key.)
In a Caesar cipher, each letter of the alphabet is shifted along some number of places. For example, in a Caesar cipher of shift 3, A would become D, B would become E, Y would become B and so on. The Vigenère cipher has several Caesar ciphers in sequence with different shift values.
To encrypt, a table of alphabets can be used, termed a tabula recta, Vigenère square or Vigenère table. It has the alphabet written out 26 times in different rows, each alphabet shifted cyclically to the left compared to the previous alphabet, corresponding to the 26 possible Caesar ciphers. At different points in the encryption process, the cipher uses a different alphabet from one of the rows. The alphabet used at each point depends on a repeating keyword.
Security :-
My question is regarding the Vigenère cipher: It is my understanding that the security of this cipher is directly related to the length and security of the keys. Long and tightly secured keys bring this cipher on par with many more complex techniques.
Besides others (e.g. random key, key used only once) it depends on the proportion of cipher text length and key length how difficult it is to break the cipher. There are tools around that can break the cipher if cipher_text_length/key_length is 4 or greater.In some exceptional cases the proportion may be even 3. Thus the Vigenere cipher is rather insecure. But as already said by others: If the key length is equal to the cipher text length then the cipher is absolutely secure if the key is chosen completely randomly and is only used once. This will turn the cipher into a one time pad. Drawback: one time pads are difficult and ineffective to manage.
Discussion
The Vigenère Cipher was the biggest step in cryptography for over
1000 years. The idea of switching between ciphertext alphabets as
you encrypt was revolutionary, and an idea that is still used to
make ciphers more secure. One of the most famous examples of codes
and ciphers in history, the ENIGMA machine, is just a modified
polyalphabetic substitution cipher!
But why is the Vigenère Cipher so secure? What is it that makes this cipher better than the Mixed Alphabet Cipher? Let's take a look at an example. We shall encrypt the following text using the Mixed Alphabet Cipher and the Vigenère Cipher, both with the keyword encrypt.
Plain Text:-
Aged twenty six, Vigènere was sent to Rome on a diplomatic mission. It was here that he became acquainted with the writings of Alberti, Trithemius and Porta, and his interest in cryptography was ignited. For many years, cryptography was nothing more than a tool that helped him his diplomatic work, but at the age of thirty nine, Vigènere decided that he had amassed enough money to be able to abandon his career and concentrate on a life of study. It was only then that he began research into a new cipher.
Using the Mixed Alphabet we get:
ETYR QVYIQX OBW, UBTYIYMY VEO OYIQ QJ MJHY JI E RBKGJHEQBC HBOOBJI. BQ VEO AYMY QAEQ AY NYCEHY ECLSEBIQYR VBQA QAY VMBQBITO JP EGNYMQB, QMBQAYHBSO EIR KJMQE, EIR ABO BIQYMYOQ BI CMXKQJTMEKAX VEO BTIBQYR. PJM HEIX XYEMO, CMXKQJTMEKAX VEO IJQABIT HJMY QAEI E QJJG QAEQ AYGKYR ABH ABO RBKGJHEQBC VJMF, NSQ EQ QAY ETY JP QABMQX IBIY, UBTYIYMY RYCBRYR QAEQ AY AER EHEOOYR YIJSTA HJIYX QJ NY ENGY QJ ENEIRJI ABO CEMYYM EIR CJICYIQMEQY JI E GBPY JP OQSRX. BQ VEO JIGX QAYI QAEQ AY NYTEI MYOYEMCA BIQJ E IYV CBKAYM.
And using the Vigenère we get:
ETGU RLXRGA JGM, OMTGECGX ANU JCCM XB TFKT HR N FZNAHQNVZA BBWFKFL. XM ANU YCGX XUCK FT UIPCDC PVUHCZLIXH JKKF IAI JTZRXGKF QW YAUIEVZ, RGBXUGDGJL EAF GMGME, NPU FXL MAVVPTLX VP TPNIXBIIYEAC JCJ GVGMGGU. DDK QNPP WTTVF, EIWEMSTTRNWR ANU EMIAMAI DMGX XUCE Y IHSY VYYI AIYRVB WBQ UKJ BXIPBORRXV ABTB, ZJM EG VYC PZI BH KFXKXL PZLT, OMTGECGX HREZBTW XUCK FT AEQ CDYHLIQ GEMJZL ZQECN MS OG RZAX XB CSYCWSA JZQ RTVRGI YCW GBPTCCMVNVV MC T PVHV MU LXHFP. GI PEF QEJN MLRP KFPM LR DVEPG VRUVYGVL VPKM P GIJ EZNWXV.
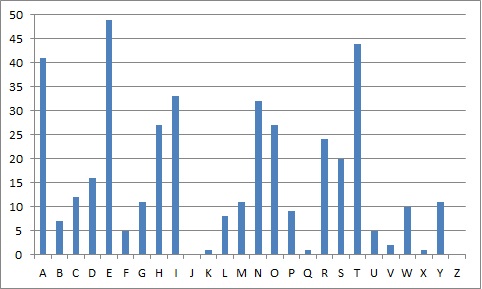
The Frequency distribution of the plaintext. 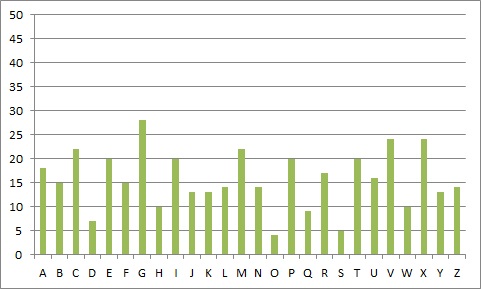
The Frequency distribution of the ciphertext using the Vigenère Cipher. |
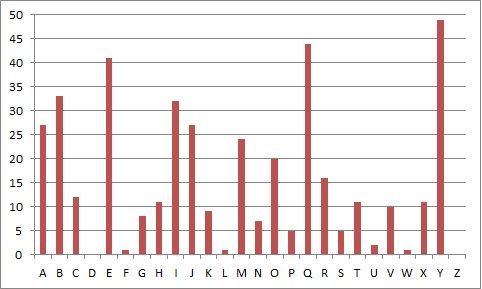
The Frequency distribution of the ciphertext using the Mixed Alphabet Cipher. These frequency distributions show how many times each letter appears in the relevent text. We can see a clear relationship between the top two, with the same peaks just in different places. |
The final distribution, for the Vigenère Cipher, is different to the others, and the distribution of letters is much more smoothed out. And even though there is a little bit of a peak at "G" (which we might think to be "e"), in the penultimate word "new" is "GIJ", so "G" is "n", but in the first word "aged" is "ETGU" so "G" is "e". This shows that the same letter can be achieved by different plaintext letters.
Add Answer to:
Suppose we have a wheel cipher device that has 4 wheels. Compare
the theoretical and practical...
modes. + There cise 4 different types o Block cipher with their advantages and disadvantages? compare...
 modes. + There cise 4 different types o Block cipher with their advantages and disadvantages? compare diferent block capher modes 2. you need to do some research on dofferent types of cryptagraphy libranes on Python. how can we use cryptography Hibranes on Python. While down the steps to install cryptography library in Python. Write a program then cry hot and decng pt a Message using Python library
modes. + There cise 4 different types o Block cipher with their advantages and disadvantages? compare diferent block capher modes 2. you need to do some research on dofferent types of cryptagraphy libranes on Python. how can we use cryptography Hibranes on Python. While down the steps to install cryptography library in Python. Write a program then cry hot and decng pt a Message using Python library
Static Equilibrium Lab: Wheel and Axle If you wanted to lift something heavy using this device, w...
 Static Equilibrium Lab: Wheel and Axle
If you wanted to lift something heavy using this device, would
you have the heavy object connected to the larger disc and then
pull one the smaller disc, or vice-versa? Why? What would be the
effect of using this device on the speed that the object lifts?
That is, if you pulled your string at a speed of 10 cm/s, would the
object lift 10 cm/s, or would it lift faster or slower?
Activity...
Static Equilibrium Lab: Wheel and Axle
If you wanted to lift something heavy using this device, would
you have the heavy object connected to the larger disc and then
pull one the smaller disc, or vice-versa? Why? What would be the
effect of using this device on the speed that the object lifts?
That is, if you pulled your string at a speed of 10 cm/s, would the
object lift 10 cm/s, or would it lift faster or slower?
Activity...
We have learned a famous shift cipher called Caesar Cipher. Now if we are given a...
We have learned a famous shift cipher called Caesar Cipher. Now if we are given a plain test: THE ART OF WARAnd key = 3 (a shift by 3 letters), please give the ciphertext Given an 8 bit block P = 10101111 and a key K = 01101011, please give the result of bitwise XOR between P and K Please give the left 2 shift of the 8 bit text 01100101 Use the given a permutation table 23614857 to define...
Before coming to lab, consider the following problem: Suppose a solid wheel (cylinder) rolls along a...
 Before coming to lab, consider the following problem: Suppose a solid wheel (cylinder) rolls along a horizontal sandy surface without slipping as it rolls it traces out a path in the sand. We wish to measure the length of the path in the sand, and all we know is the radius of the cylindrical wheel, and the angle through which the wheel rolls. The wheel has a measured radius of 45 + 4 cm is seen to rotate through an...
Before coming to lab, consider the following problem: Suppose a solid wheel (cylinder) rolls along a horizontal sandy surface without slipping as it rolls it traces out a path in the sand. We wish to measure the length of the path in the sand, and all we know is the radius of the cylindrical wheel, and the angle through which the wheel rolls. The wheel has a measured radius of 45 + 4 cm is seen to rotate through an...
1. Suppose that we catch either salmon (state 1) or sea bass (state 2) according to a Markov Model where the transition matrix is given by 0.8 0.2 A= 0.4 0.6 Suppose that we compare the length, x, of...
 1. Suppose that we catch either salmon (state 1) or sea bass (state 2) according to a Markov Model where the transition matrix is given by 0.8 0.2 A= 0.4 0.6 Suppose that we compare the length, x, of each fish that we catch to 15cm, and that for all times P(x> 15| salmon) 0.2 P(x > 15 sea bass) 0.7 (a) Suppose we caught a salmon at time 1. What is the probability that we catch a sea bass...
1. Suppose that we catch either salmon (state 1) or sea bass (state 2) according to a Markov Model where the transition matrix is given by 0.8 0.2 A= 0.4 0.6 Suppose that we compare the length, x, of each fish that we catch to 15cm, and that for all times P(x> 15| salmon) 0.2 P(x > 15 sea bass) 0.7 (a) Suppose we caught a salmon at time 1. What is the probability that we catch a sea bass...
Something is Amiss in the Purchasing Department at The Wheel Drive The Wheel Drive has been...
Something is Amiss in the Purchasing Department at The Wheel Drive The Wheel Drive has been a profitable company since it was founded 10 years ago. At the start of the last financial year, the company had doubled the number of employees from the year before. Wheel Drive hired and trained employees for a specialized Purchasing Department. The Purchasing Department’s main role is to purchase raw materials required for the production of specialized car hubcaps and wheels sold to old...
Question 29 7 pts Suppose we have a byte-addressable computer with a cache that holds 8...
 Question 29 7 pts Suppose we have a byte-addressable computer with a cache that holds 8 blocks of 4 bytes each. Assuming that each memory address has 8 bits, to which cache block would the hexadecimal address Ox1F map if the computer uses direct mapping?
Question 29 7 pts Suppose we have a byte-addressable computer with a cache that holds 8 blocks of 4 bytes each. Assuming that each memory address has 8 bits, to which cache block would the hexadecimal address Ox1F map if the computer uses direct mapping?
4-116 Suppose we wish to test the hypothesi s Ho: u WILEY versus the alternative : > 85 where T-1...
 4-116 Suppose we wish to test the hypothesi s Ho: u WILEY versus the alternative : > 85 where T-16. Suppose that the true mean is μ 86 and that in the practical context of the -85 that has practical problem this is not a departure from μ0 significance (a) For a test with α 0.01, compute β for the sample sizes n-25, 100, 400, and 2500 assuming that μ-86 (b) Suppose the sample average is x - 86. Find...
4-116 Suppose we wish to test the hypothesi s Ho: u WILEY versus the alternative : > 85 where T-16. Suppose that the true mean is μ 86 and that in the practical context of the -85 that has practical problem this is not a departure from μ0 significance (a) For a test with α 0.01, compute β for the sample sizes n-25, 100, 400, and 2500 assuming that μ-86 (b) Suppose the sample average is x - 86. Find...
pls both 31 Question 31 10 pts Suppose we have a byte-addressable computer using 4-way set...
 pls both 31
Question 31 10 pts Suppose we have a byte-addressable computer using 4-way set associative mapping with 24-bit main memory addresses and 64 blocks of cache. Suppose also that a block contains 32 bytes. The size of the block offset field is bits, the size of the set field is bits, and the size of the tag field is bits. Question 32 1 pts is the oldest and most cost-effective of all mass-storage devices. Magnetic tape Compact dick...
pls both 31
Question 31 10 pts Suppose we have a byte-addressable computer using 4-way set associative mapping with 24-bit main memory addresses and 64 blocks of cache. Suppose also that a block contains 32 bytes. The size of the block offset field is bits, the size of the set field is bits, and the size of the tag field is bits. Question 32 1 pts is the oldest and most cost-effective of all mass-storage devices. Magnetic tape Compact dick...
1. Suppose we have a fair die that has twelve (12) sides. That is, if we...
1. Suppose we have a fair die that has twelve (12) sides. That is, if we roll it, each of the first 12 positive integers are equally likely to be the result of the roll. (a) If we roll the die, what is the probability the result is prime? As a reminder, one is not a prime number. (b) Suppose we roll this die 1000 times. What is the probability we get a prime number exactly 200 times? (c) Suppose...
Most questions answered within 3 hours.
-
Write a program that reads in a text file, infile.txt, and
prints out all the lines...
asked 2 hours ago -
Which of the following orbits have a total of zero energy (based
on the common convention)?...
asked 2 hours ago -
Find the expected count and the contribution to the chi-square
statistic for the (Group 1, No)...
asked 3 hours ago -
Suppose you are purchasing a meal and with every meal a you
receive one of 10...
asked 3 hours ago -
A 75.0 kg 0erson is riding in a car moving at 20.0 m/s when the
car...
asked 3 hours ago -
What does Δp = QR mean in words?
Pushing a viscous fluid through a pipe requires...
asked 3 hours ago -
We know that system.out.println (“object number” + n ); is
legal.String name; int n; name =...
asked 3 hours ago -
Come up with a real-life problem (open-ended) and solve it by
designing and writing a Java...
asked 3 hours ago -
Power Music owns five music stores, where it sells music,
instruments, and supplies. In addition, it...
asked 4 hours ago -
True or false and
why:
Given the following sequence of numbers to be
inserted {4,5,6,1,2,3,8,7}, the...
asked 4 hours ago -
Code using Java
What is an interface? Complete the following code:
interface IExample{
public void print();...
asked 4 hours ago -
Bob Nale is the owner of Nale’s Quick Fill. Bob would like to
estimate the mean...
asked 4 hours ago
 modes. + There cise 4 different types o Block cipher with their advantages and disadvantages? compare diferent block capher modes 2. you need to do some research on dofferent types of cryptagraphy libranes on Python. how can we use cryptography Hibranes on Python. While down the steps to install cryptography library in Python. Write a program then cry hot and decng pt a Message using Python library
modes. + There cise 4 different types o Block cipher with their advantages and disadvantages? compare diferent block capher modes 2. you need to do some research on dofferent types of cryptagraphy libranes on Python. how can we use cryptography Hibranes on Python. While down the steps to install cryptography library in Python. Write a program then cry hot and decng pt a Message using Python library
 Static Equilibrium Lab: Wheel and Axle
If you wanted to lift something heavy using this device, would
you have the heavy object connected to the larger disc and then
pull one the smaller disc, or vice-versa? Why? What would be the
effect of using this device on the speed that the object lifts?
That is, if you pulled your string at a speed of 10 cm/s, would the
object lift 10 cm/s, or would it lift faster or slower?
Activity...
Static Equilibrium Lab: Wheel and Axle
If you wanted to lift something heavy using this device, would
you have the heavy object connected to the larger disc and then
pull one the smaller disc, or vice-versa? Why? What would be the
effect of using this device on the speed that the object lifts?
That is, if you pulled your string at a speed of 10 cm/s, would the
object lift 10 cm/s, or would it lift faster or slower?
Activity...
 Before coming to lab, consider the following problem: Suppose a solid wheel (cylinder) rolls along a horizontal sandy surface without slipping as it rolls it traces out a path in the sand. We wish to measure the length of the path in the sand, and all we know is the radius of the cylindrical wheel, and the angle through which the wheel rolls. The wheel has a measured radius of 45 + 4 cm is seen to rotate through an...
Before coming to lab, consider the following problem: Suppose a solid wheel (cylinder) rolls along a horizontal sandy surface without slipping as it rolls it traces out a path in the sand. We wish to measure the length of the path in the sand, and all we know is the radius of the cylindrical wheel, and the angle through which the wheel rolls. The wheel has a measured radius of 45 + 4 cm is seen to rotate through an...
 1. Suppose that we catch either salmon (state 1) or sea bass (state 2) according to a Markov Model where the transition matrix is given by 0.8 0.2 A= 0.4 0.6 Suppose that we compare the length, x, of each fish that we catch to 15cm, and that for all times P(x> 15| salmon) 0.2 P(x > 15 sea bass) 0.7 (a) Suppose we caught a salmon at time 1. What is the probability that we catch a sea bass...
1. Suppose that we catch either salmon (state 1) or sea bass (state 2) according to a Markov Model where the transition matrix is given by 0.8 0.2 A= 0.4 0.6 Suppose that we compare the length, x, of each fish that we catch to 15cm, and that for all times P(x> 15| salmon) 0.2 P(x > 15 sea bass) 0.7 (a) Suppose we caught a salmon at time 1. What is the probability that we catch a sea bass...
 Question 29 7 pts Suppose we have a byte-addressable computer with a cache that holds 8 blocks of 4 bytes each. Assuming that each memory address has 8 bits, to which cache block would the hexadecimal address Ox1F map if the computer uses direct mapping?
Question 29 7 pts Suppose we have a byte-addressable computer with a cache that holds 8 blocks of 4 bytes each. Assuming that each memory address has 8 bits, to which cache block would the hexadecimal address Ox1F map if the computer uses direct mapping?
 4-116 Suppose we wish to test the hypothesi s Ho: u WILEY versus the alternative : > 85 where T-16. Suppose that the true mean is μ 86 and that in the practical context of the -85 that has practical problem this is not a departure from μ0 significance (a) For a test with α 0.01, compute β for the sample sizes n-25, 100, 400, and 2500 assuming that μ-86 (b) Suppose the sample average is x - 86. Find...
4-116 Suppose we wish to test the hypothesi s Ho: u WILEY versus the alternative : > 85 where T-16. Suppose that the true mean is μ 86 and that in the practical context of the -85 that has practical problem this is not a departure from μ0 significance (a) For a test with α 0.01, compute β for the sample sizes n-25, 100, 400, and 2500 assuming that μ-86 (b) Suppose the sample average is x - 86. Find...
 pls both 31
Question 31 10 pts Suppose we have a byte-addressable computer using 4-way set associative mapping with 24-bit main memory addresses and 64 blocks of cache. Suppose also that a block contains 32 bytes. The size of the block offset field is bits, the size of the set field is bits, and the size of the tag field is bits. Question 32 1 pts is the oldest and most cost-effective of all mass-storage devices. Magnetic tape Compact dick...
pls both 31
Question 31 10 pts Suppose we have a byte-addressable computer using 4-way set associative mapping with 24-bit main memory addresses and 64 blocks of cache. Suppose also that a block contains 32 bytes. The size of the block offset field is bits, the size of the set field is bits, and the size of the tag field is bits. Question 32 1 pts is the oldest and most cost-effective of all mass-storage devices. Magnetic tape Compact dick...