Answer the following questions related to Access Control Lists (ACLs): Why do we require access list?...
Answer the following questions related to Access Control Lists (ACLs):
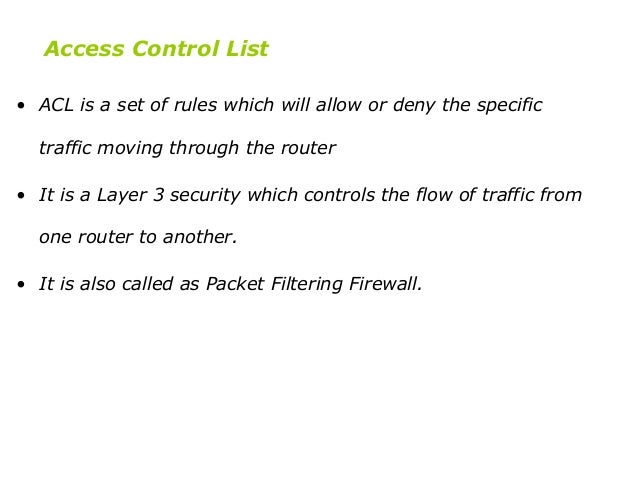
- Why do we require access list?
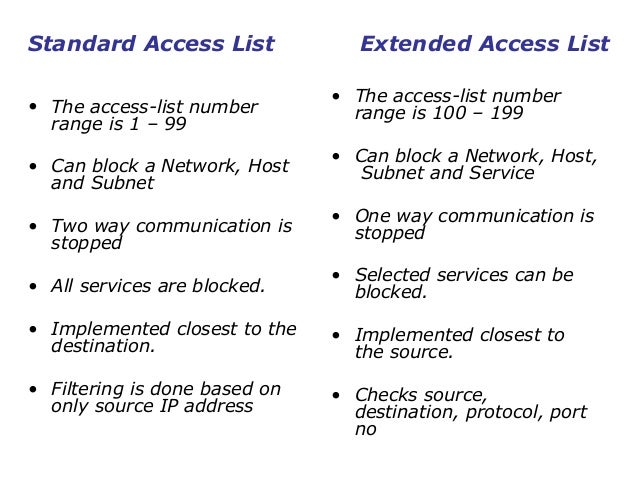
- What is difference between standard access lists and extended?
- What is difference between ACL and firewall?
Homework Answers


Add Answer to:
Answer the following questions related
to Access Control Lists (ACLs):
Why do we require access list?...
FTP requires two ports to be defined in the access control list, why is this? Should...
FTP requires two ports to be defined in the access control list, why is this? Should basic ACL and advanced ACL be deployed near the source network or target network, and why?
Complete the following short answer questions: 1. How do the viruses propagate between computers? 2. What is social...
Complete the following short answer questions: 1. How do the viruses propagate between computers? 2. What is social engineering? 3. How will an SPI firewall handle a packet containing a TCP segment which is an acknowledgement? 4. Revise the access control list (ACL) in Figure 3-23 (page 119 in the textbook) to permit access to an FTP server with IP address 10.32.67.112. 5. How will the ACL in Figure 3-23 (page 119 in the textbook) handle a packet that attempts to open a connection to...
A small financial firm is currently using ACL (Access Control List), a discretionary access control mechanism, for the protection of its resources (including computer systems and data files). As...
 A small financial firm is currently using ACL (Access Control List), a discretionary access control mechanism, for the protection of its resources (including computer systems and data files). As the firm is small, its resources are located in the same building and managed in the same domain. However, recently this firm is planning a merger with another firm, and if this merger is successful, its IT system will be transformed into a large-scale distributed system where resources will be managed...
A small financial firm is currently using ACL (Access Control List), a discretionary access control mechanism, for the protection of its resources (including computer systems and data files). As the firm is small, its resources are located in the same building and managed in the same domain. However, recently this firm is planning a merger with another firm, and if this merger is successful, its IT system will be transformed into a large-scale distributed system where resources will be managed...
II. Short Answer - The following questions require either brief lists or 3 or 4 sentence...
II. Short Answer - The following questions require either brief lists or 3 or 4 sentence answers at most. For questions that require lists, any incorrect item will be marked as such. That is, if the question asks for three items and you list four, you will not receive credit if one of those four is incorrect. What are some of the concerns related to subsidizing anti-malarial drugs?
Question 2: Answer the following questions related to Firewall Technologies: What are the types of firewalls?...
Question 2: Answer the following questions related to Firewall Technologies: What are the types of firewalls? What are security zones? What is a firewall DMZ?
41) Firewalls use which of the fo a) Cross Site Scripting CKSS) b) Access Control Lists...
 41) Firewalls use which of the fo a) Cross Site Scripting CKSS) b) Access Control Lists (ACL) e)Exploits (EXP) d)Hashes (HSS) ng to control traffic? 42) What is the primary function of a router? a) To prevent Distributed Denial of Service (DDoS) attacks. b) To map MAC addresses to ports. c)To interconnect workstations to switches. d)To interconnect networks. 43) Which statements are true about rainbow tables? (Select all that apply) A. You can build a rainbow table once and reuse...
41) Firewalls use which of the fo a) Cross Site Scripting CKSS) b) Access Control Lists (ACL) e)Exploits (EXP) d)Hashes (HSS) ng to control traffic? 42) What is the primary function of a router? a) To prevent Distributed Denial of Service (DDoS) attacks. b) To map MAC addresses to ports. c)To interconnect workstations to switches. d)To interconnect networks. 43) Which statements are true about rainbow tables? (Select all that apply) A. You can build a rainbow table once and reuse...
b) Answer the following questions related to titration technique i) What is differenc
b) Answer the following questions related to titration technique i) What is difference between acidimetry and alkalimetry titrations? ii) What is an indicator? iii) Write any two properties of primary standard substance.
Answer the following questions related to the given electrochemical cell. Answer the following questions related to...
 Answer the following questions related to the given
electrochemical cell.
Answer the following questions related to the given electrochemical cell 2NO(g) H20(l) 2e N20(g) 20H (aq) 0.760 V NO aq) H2O(l) 2e NO2 (aq) 20H (aq) Eo 0.010 V 1. Answer the following questions under standard conditions (a) The half cell containing N20/NO is the (b) The half cell containing NO3 /NO2 s the (c) What is Eocell (in V)? Report your answer to three decimal places in standard notation...
Answer the following questions related to the given
electrochemical cell.
Answer the following questions related to the given electrochemical cell 2NO(g) H20(l) 2e N20(g) 20H (aq) 0.760 V NO aq) H2O(l) 2e NO2 (aq) 20H (aq) Eo 0.010 V 1. Answer the following questions under standard conditions (a) The half cell containing N20/NO is the (b) The half cell containing NO3 /NO2 s the (c) What is Eocell (in V)? Report your answer to three decimal places in standard notation...
79. Access the 2018 form 10-K for Facebook, Inc, and answer the following questions. Required: a)...
79. Access the 2018 form 10-K for Facebook, Inc, and answer the following questions. Required: a) Using information from the company's Income Statement and Income Taxes footnote, what was the company's effective tax rate for 2018? Show how the rate is calculated. b) Using information from the Statement of Cash flows, calculate the company's cash tax rate. c) What does the company's Income Tax note tell you about where the company earns its international income? Why does earning income in...
An LTI system has the signal flow graph shown below. Answer the following related questions. .3 a...
 An LTI system has the signal flow graph shown below. Answer the following related questions. .3 a) Determine the relation(i.e., difference equation) between x[n] and w[n] b) Determine the relation (i.e., difference equation) between win] and y[n] c) Determine the difference equation of the above system (i.e., overall system) d) Determine the system function of the overall system. Plot the pole-zero diagram. If this is known to be a non-causal and non-stable system, indicate the ROC. e) Draw the direct...
An LTI system has the signal flow graph shown below. Answer the following related questions. .3 a) Determine the relation(i.e., difference equation) between x[n] and w[n] b) Determine the relation (i.e., difference equation) between win] and y[n] c) Determine the difference equation of the above system (i.e., overall system) d) Determine the system function of the overall system. Plot the pole-zero diagram. If this is known to be a non-causal and non-stable system, indicate the ROC. e) Draw the direct...
Most questions answered within 3 hours.
-
HELP WITH SAS
Run the following DATA step to create a SAS data set called
ABC_CORP....
asked 9 minutes ago -
A researcher wishes to study the cumulative effects of several
combinations of HIV drugs. There are...
asked 29 minutes ago -
How
to make a simple game of whack a mole in pygame
asked 12 minutes ago -
Write a c/c++ program to read a list of students from a file and
create a...
asked 21 minutes ago -
Identify two different methods for collecting data in
qualitative research. What are the benefits and challenges...
asked 22 minutes ago -
I am suppose to have my array before the main class but I am
getting the...
asked 24 minutes ago -
Your task is to design the page table for the 32bit Pentium
microprocessor. Answer the following...
asked 30 minutes ago -
The Paradise Shoes Company has estimated its weekly TVC function
from data collected over the past...
asked 29 minutes ago -
Although Epicurus advocates pursuing pleasure for the
good life, discuss a few reasons why he does...
asked 46 minutes ago -
Problem 1: Present entries to record the selected transactions
described below:
(a)
Issued $2,790,000 of 5-year,...
asked 53 minutes ago -
Using technology to support HR activities increases:
a.
the efficiency of the administrative HR functions.
b....
asked 53 minutes ago -
1. List the features used to classify leaf
types.
2. List some characteristics that are shared...
asked 58 minutes ago
 A small financial firm is currently using ACL (Access Control List), a discretionary access control mechanism, for the protection of its resources (including computer systems and data files). As the firm is small, its resources are located in the same building and managed in the same domain. However, recently this firm is planning a merger with another firm, and if this merger is successful, its IT system will be transformed into a large-scale distributed system where resources will be managed...
A small financial firm is currently using ACL (Access Control List), a discretionary access control mechanism, for the protection of its resources (including computer systems and data files). As the firm is small, its resources are located in the same building and managed in the same domain. However, recently this firm is planning a merger with another firm, and if this merger is successful, its IT system will be transformed into a large-scale distributed system where resources will be managed...
 41) Firewalls use which of the fo a) Cross Site Scripting CKSS) b) Access Control Lists (ACL) e)Exploits (EXP) d)Hashes (HSS) ng to control traffic? 42) What is the primary function of a router? a) To prevent Distributed Denial of Service (DDoS) attacks. b) To map MAC addresses to ports. c)To interconnect workstations to switches. d)To interconnect networks. 43) Which statements are true about rainbow tables? (Select all that apply) A. You can build a rainbow table once and reuse...
41) Firewalls use which of the fo a) Cross Site Scripting CKSS) b) Access Control Lists (ACL) e)Exploits (EXP) d)Hashes (HSS) ng to control traffic? 42) What is the primary function of a router? a) To prevent Distributed Denial of Service (DDoS) attacks. b) To map MAC addresses to ports. c)To interconnect workstations to switches. d)To interconnect networks. 43) Which statements are true about rainbow tables? (Select all that apply) A. You can build a rainbow table once and reuse...
 Answer the following questions related to the given
electrochemical cell.
Answer the following questions related to the given electrochemical cell 2NO(g) H20(l) 2e N20(g) 20H (aq) 0.760 V NO aq) H2O(l) 2e NO2 (aq) 20H (aq) Eo 0.010 V 1. Answer the following questions under standard conditions (a) The half cell containing N20/NO is the (b) The half cell containing NO3 /NO2 s the (c) What is Eocell (in V)? Report your answer to three decimal places in standard notation...
Answer the following questions related to the given
electrochemical cell.
Answer the following questions related to the given electrochemical cell 2NO(g) H20(l) 2e N20(g) 20H (aq) 0.760 V NO aq) H2O(l) 2e NO2 (aq) 20H (aq) Eo 0.010 V 1. Answer the following questions under standard conditions (a) The half cell containing N20/NO is the (b) The half cell containing NO3 /NO2 s the (c) What is Eocell (in V)? Report your answer to three decimal places in standard notation...
 An LTI system has the signal flow graph shown below. Answer the following related questions. .3 a) Determine the relation(i.e., difference equation) between x[n] and w[n] b) Determine the relation (i.e., difference equation) between win] and y[n] c) Determine the difference equation of the above system (i.e., overall system) d) Determine the system function of the overall system. Plot the pole-zero diagram. If this is known to be a non-causal and non-stable system, indicate the ROC. e) Draw the direct...
An LTI system has the signal flow graph shown below. Answer the following related questions. .3 a) Determine the relation(i.e., difference equation) between x[n] and w[n] b) Determine the relation (i.e., difference equation) between win] and y[n] c) Determine the difference equation of the above system (i.e., overall system) d) Determine the system function of the overall system. Plot the pole-zero diagram. If this is known to be a non-causal and non-stable system, indicate the ROC. e) Draw the direct...